
The ultimate (and only true) Way to Ransomware Recovery
This article was originally published in www.v2cloud.com
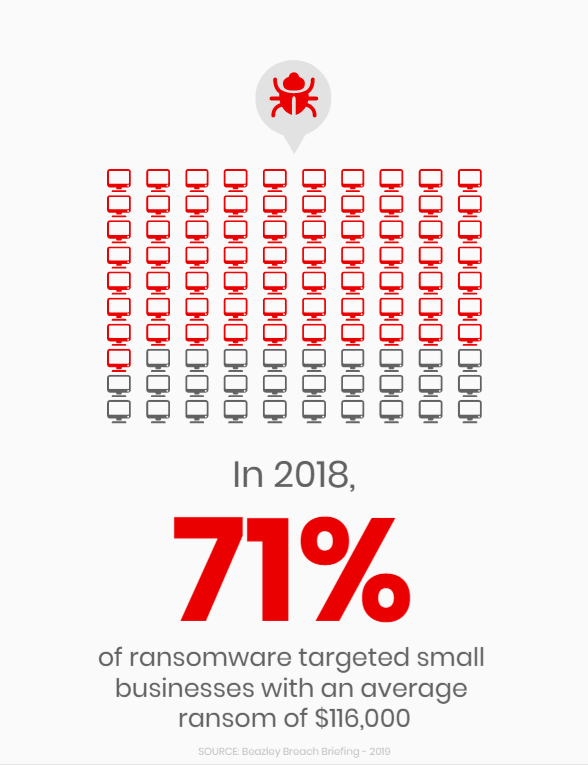
Businesses are paying an average of $133k to recover from a ransomware, and it’s not only happening to “others”. Everybody is looking for a ransomware recovery solution a little too late.
Last month, I had a long conversation with John, a partner of a 24-employee law firm in New York. They reached out to us a few weeks after recovering from a ransomware attack. When I say recovering, I don’t mean without any bruises…
Here’s their story.
They thought they were protected from cyberattacks. They had an antivirus in place, all their data was properly backed up in Cloud storage (OneDrive with Office 365) and their management software is a SaaS web application.
What else do they need, right?
So Monday morning, the receptionist opens an email from one of their clients. She suspected nothing since she knew where the email came from.
Turns out, ransomware had infected that client and the virus crawled its way through the Outlook contacts. Oh, it also got through all of their Skype contacts as well…
Within a few minutes, her computer is encrypted, like every other computer in the office. Yep, these things crawl through all computers in an office network in no time.
Twenty-two desktop computers completely encrypted and unusable, with a friendly 72 hours countdown beeping on the screen and a bitcoin address at the bottom. On top of that, the virus silently started sending itself through all of their business contacts.
So at this point, the panic spreads across the office. Another partner, Chris, called the number on the screen to find out their options.
Apparently, the underground company responsible for the attack had really good “customer service”.
They calmly explained that the computers were encrypted and the only way to get them back is to pay the ransom – about 0.8 bitcoins – or $50 400 USD– (as of October 2021) transferred into 34 random characters, untraceable Bitcoin address.

A typical bitcoin address
What did they do?
Chris then called their IT firm, the one that manages their printers and offers occasional IT support, asking for advice.
They strongly suggested to not pay the ransom, as they have very little chance to recover their data from it and absolutely no assurance that this would not happen again in the future.
They decided not to pay the ransom and instead get help from the IT firm to recover from their backups. On the same day, two technicians came over to work on it.
They first looked for ways to get rid of the virus. They quickly concluded that this was hopeless – these parasites are relentless.
You can’t even open Chrome on an infected computer.
They had to replace all 22 computers, reconfigure the network, reinstall all applications, configure printer drivers, set up user credentials, restore their backups, reconfigure new backups, and so on.
It took a week just for the employees to regain access to their work computer, plus another week to resume running at normal speed.
So I asked John: How much did it cost you to replace all hardware in the office?
“The hardware? I don’t know… maybe $15k with the IT firm invoice. But who cares about that? We lost over $80,000 in billable hours being down for a week. And a LOT of angry customers. We almost lost our business because of this s***.”
Wow. $100k for a computer virus. It is getting serious nowadays.
The way to Ransomware Recovery
- You need to choose the best antivirus for you.
- You need a solid file backup solution.
- You need a password manager for sharing passwords and protect valuable data.
- You need to educate your employees about cybersecurity risks and best practices.
But ultimately, you also need a last resort ransomware recovery plan. Just like you need an ejection seat in a Lockheed Martin F-35 jet, for, you know, when things turn unexpected, you need a disaster recovery plan in any modern-day business.
The kind of plan that you can press a button and get back your computers running like they were last night. A REAL ransomware attack solution.
You need snapshots.

Snapshots are the ejection seat of the disaster recovery plan for your business. A snapshot is a complete system backup of a computer separated from the main disk image.
In case of disaster, when the virus infected all the computer systems and everything is encrypted, you can revert in time to a previous snapshot. And since this is done at the hypervisor level, it’s immune against ransomware.
For your business to benefit from snapshots, you need a VDI environment. Either on-premise or in the Cloud (also called DaaS- such as the 2iBi Primavera Cloud), as long as there is a mechanism in place to take snapshots daily.
And those snapshots need to be monitored and properly tested for integrity, obviously.
This is the last resort safety mechanism needed after all your efforts to prevent these ransomware attacks. You might never have to use the airbags of your car, and hopefully, you will never, but you still need them.
Those airbags would have cost John about $850/mo for 24 users instead of $100,000 in costs and lost revenues. John’s firm luckily was able to survive and if they ever experienced a cyber-attack again, they have a safety net.
That’s why it is so important to choose wisely the software you use in your business. When we develop 2iBi’s Primavera Cloud we could not avoid to use a Daas solution as a guide.
Thus we were able to still perform and efficiently help our clients always keeping safety as a priority. If you want to know more and book a free live demo of 2iBi Primavera Cloud®, click here

Mathieu Ferland
Founder and CEO of V2 Cloud

